What Step Is Part of Reporting of Security Incidents
CNotify Business Associates and Trading Partners of the breach. Incident Response Step 2 Response.
6 Incident Response Steps To Take After A Security Event
However 164314 a 2 i C and b 2 iv require contracts between a covered entity and a business associate and plan documents of a group health plan.
. Security Incident Reporting Procedures Step 1 Report Crime to local law enforcement if required. Its a motto that is also highly relevant to ensuring that our systems and data are secure. The next step is arguably the most important and official of all the steps and ensures that the immediate manager and any authorities are informed about the incident.
-What step is part of reporting of security incidents. The bulk of the effort in properly. The update to FISMA is an important first step toward solving supply chain security problems exposed by SolarWinds rather than simply identifying them.
Step 3 Receive incident determination from CDA Program Manager. Quantify Significant Cyber Incidents. Be sure to have your lines ready in case they contact.
Identify potential security incidents through monitoring and report all incidents. You need to make sure that it is immediately reported so that people can remain protected from any knock-on damage that might occur. Security incidents are on the rise coming from a multitude of directions and in many guises.
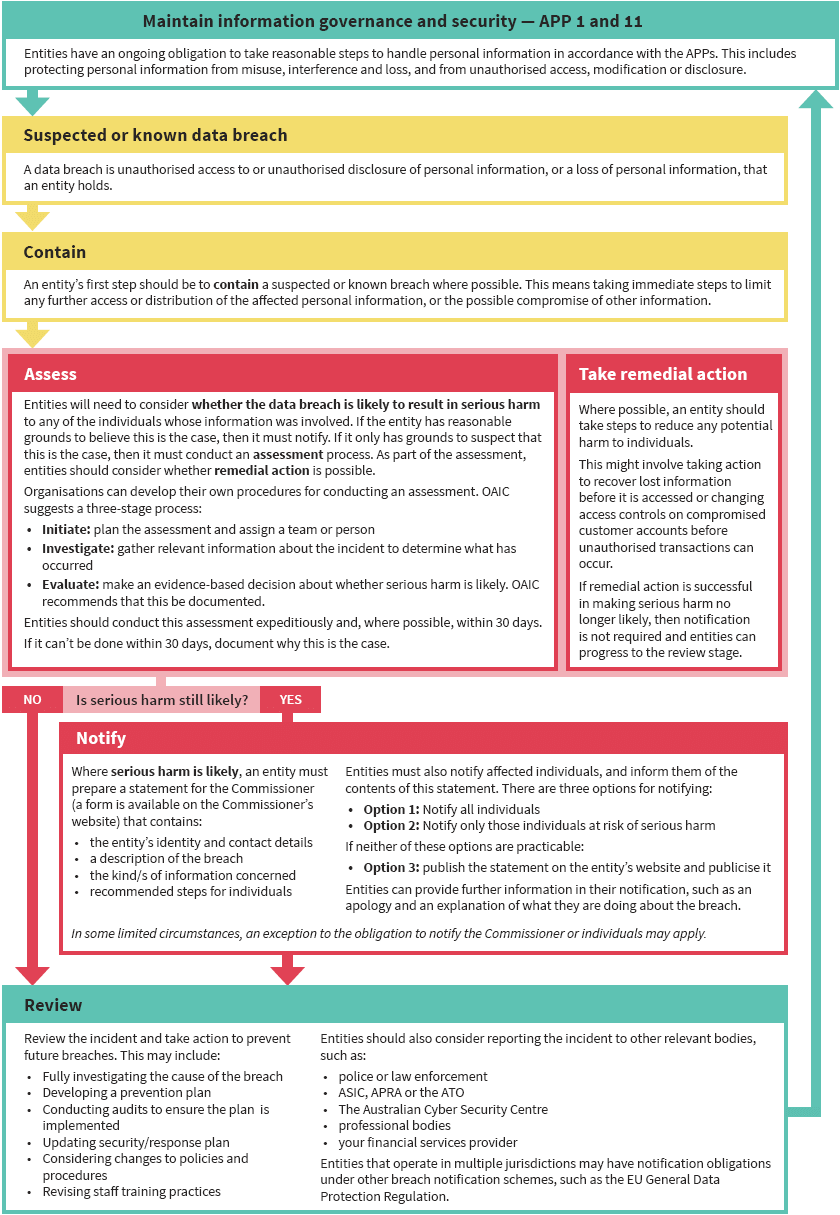
Incident reporting plays an important role in these efforts as it contributes in improving stakeholders knowledge of the actual security problems at stake. This helps to limit damage the quicker the. Step 2 Complete Security Incident Report.
In order to have an effective cyber security program you need eyes and ears everywhere. The update to FISMA is an important first step toward solving supply chain security problems exposed by SolarWinds rather than simply identifying them. Information security incident refers to an adverse event in an information system network andor workstation or the threat of the occurrence of such an event.
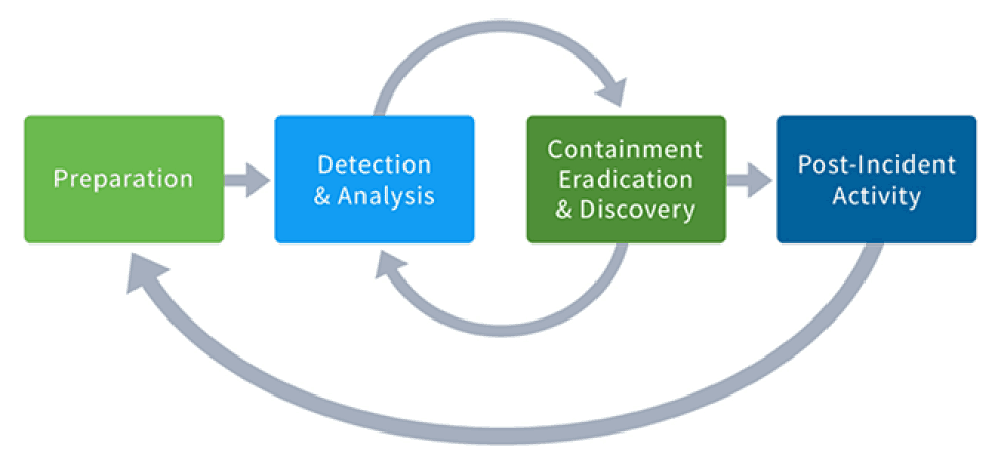
If you see something say something is the motto of the Department of Homeland Security. As part of the EO and existing FISMA statute Federal Civilian Executive Branch FCEB agencies are required to report significant breaches. Incident response IR is a structured methodology for handling security incidents breaches and cyber threats.
This in-depth look at the nature of the threat and the best ways to respond to it now is essential reading for any security professional. An effective incident reporting system contributes to the collection of reliable and up-to-date data on information security incidents and ensures. Definitions Information Security Incident.
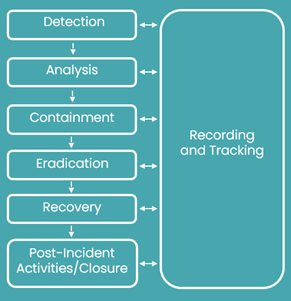
Does the reported incident meet the criteria for. Your reporting process should include accommodation for regulatory reporting escalations. Analysts create an incident ticket document initial findings and assign an initial incident classification.
Report all suspected or confirmed Security Incidents Immediately. The information security incident reporting form is an important first step in handling information security incidents in a coordinated response. IDS Security Services must provide clearance to reconnect or use a system that has been part of an incident investigation and recovery suspected or confirmed.
SECURITY INCIDENT REPORTING PROCEDURES ReportallsuspectedorconfirmedSecurityIncidentsImmediately TheUniversityofMassachusettsMedical. Step 4 Reporting person coordinates with. Technology Examination Handbook IT Handbook on Information Security management should define thresholds for reporting security incidents internally and develop processes for when the institution should notify its regulator of incidents that may affect the institutions operations reputation or sensitive customer information.
Prepare for handling incidents. -What step is part of reporting of security incidents. BExclude notation of incident from the patients medical record.
Building one incident process. The Importance of Security Incident Reporting. Activate a Computer Security Incident Response Team CIRT to investigate assess the damage collect evidence report the incident and perform recovery procedures.
AReport disclosure to all patients. The ISOIEC Standard 27035 outlines a five-step process for security incident management including. Detect potential security incidents by correlating alerts within a SIEM solution.
Once youve double-checked the security incident report youve written and youre confident that everything in the report is true and correct it is now time to submit your report to the investigator or to the authorities so they can begin their investigation and provide their appropriate recommendation report and feedback. Reporting Critical Cyber Security Incidents. While internal reporting of security incidents is an inherent part of security incident policies and procedures the Security Rule generally does not require a covered entity to report incidents to outside entities.
Finance where operators need to report incidents to regulators. Assess identified incidents to determine the appropriate next steps for mitigating the risk. Incident reporting should be part of a bi-directional flow of information where providers report about security incidents to authorities and authorities feedback common threats and common issues to the cloud providers so they can improve security and resilience.
A well-defined incident response plan IRP allows you to effectively identify minimize the damage from and reduce the cost of a cyberattack while finding and fixing the cause so that you can prevent future attacks. Users reporting a security incident will be informed of the resolution or outcome of the incident response and recovery after all investigations have been completed. Therefore incident management procedures should include initial discovery and reporting of suspected incidents or events as the first step.
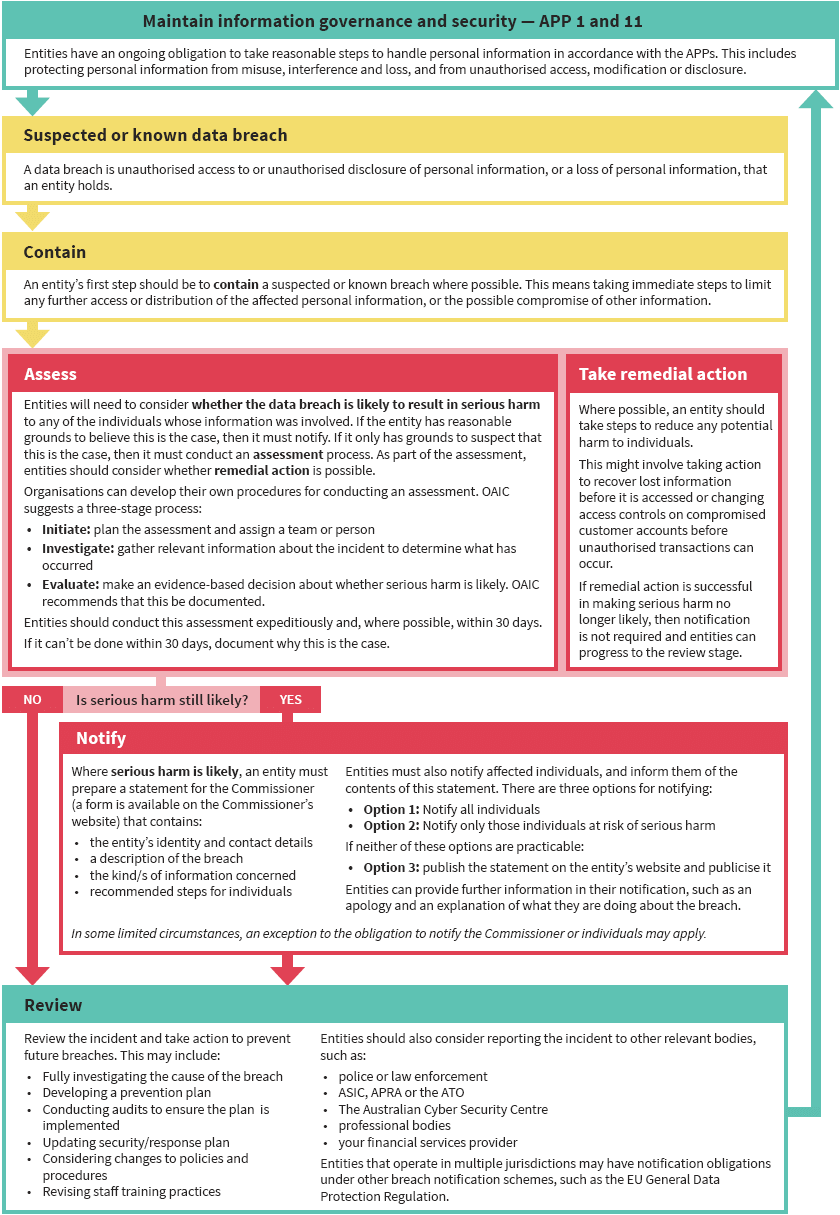
Part 3 Responding To Data Breaches Four Key Steps Home

Comments
Post a Comment